At a glance:
- Email claimed to be from Mei Leng, Sales Executive at Argus Technologies WLL, Doha-Qatar
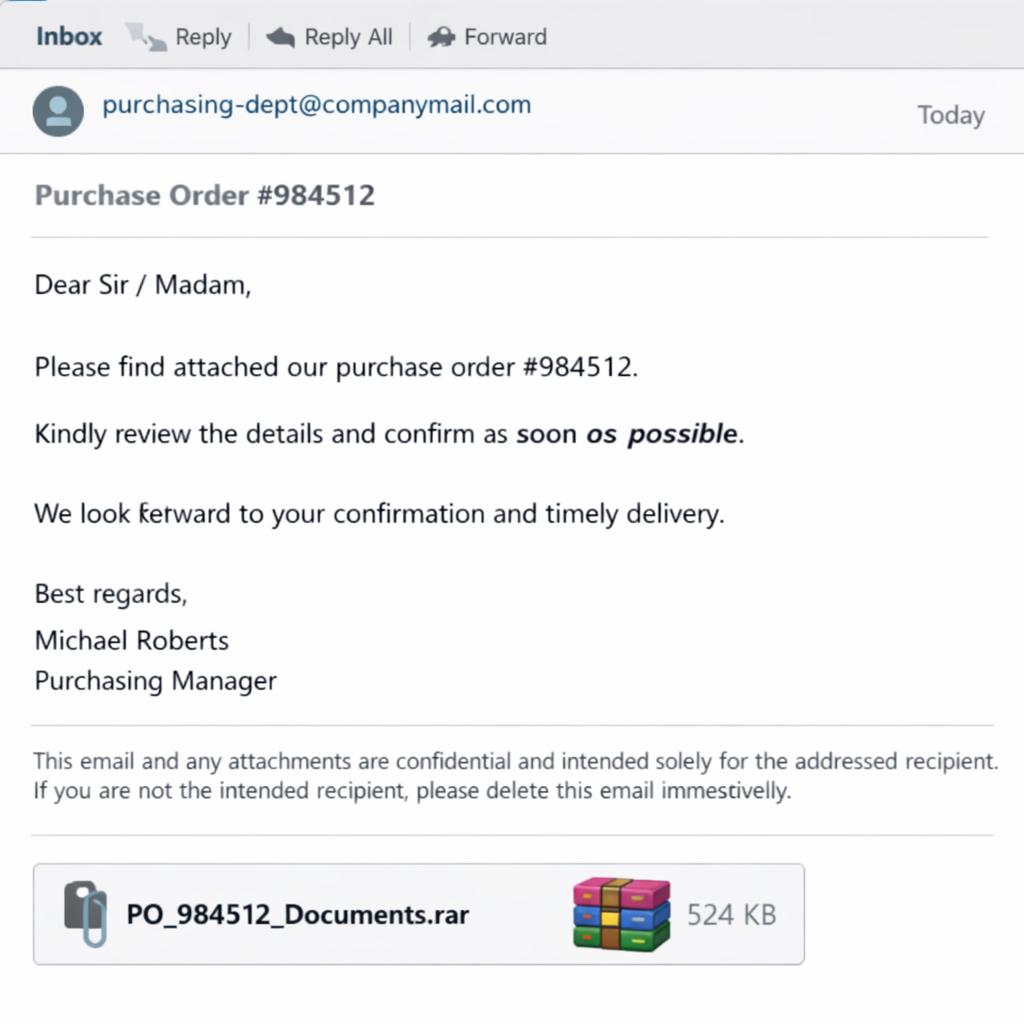
- Actual sender domain:
abv.bg— a Bulgarian consumer email service with no connection to any Qatari company - Subject line opens with “RE:” to fake an ongoing conversation that never happened
- Attachment is a
.rararchive namedEDIT PI-74625463.rar— not a standard business document format - Email body asks the recipient to “check the enclosed bank detail” — the functional core of the fraud
Step 1 — Sender Analysis
The email displays as coming from Mei Leng at ikunev79@abv.bg.
ABV.bg is a Bulgarian consumer free email provider. It’s the regional equivalent of Hotmail. The claimed employer — Argus Technologies WLL — is presented as a legitimate technology company based in Doha, Qatar. A real procurement team at a Qatari company would send email from a corporate domain, not a Bulgarian webmail account. The display name “Mei Leng” and the address “ikunev79” are unrelated. One was chosen for credibility, the other was already there.
The company blog linked in the signature points to http://argustechnology.blogspot.com/ — a free Blogspot page. Not a corporate website. Not a contact us page with a verified address. A free blog that anyone can create in four minutes.
This combination — free email, free blog, no verifiable domain — is a constructed identity, not a real company.
One additional detail: the email was sent to an old, migrated store address. That address wasn’t found through research. It came from a scraped database — an outdated listing, a cached web page, or a data broker file. The attacker did not find this store specifically. They found an address and sent to it.
Step 2 — Email Body Red Flags
The “RE:” prefix is fabricated.
The subject line reads: RE: NEW ORDER FINAL INVOICE (NEW SALES GUY).
The “RE:” implies this is a reply to an existing thread. There is no existing thread. The prefix was added manually. This is a standard manipulation tactic — it’s designed to make the recipient pause before dismissing the email, because deleting a reply feels different from deleting cold outreach. That hesitation is the point.
The management change story is social engineering.
The body opens with: “We are Sorry for the delay, which is due to change in management, we can no longer wait for the return of our manager.”
This pre-explains why the communication feels off. Before the recipient can ask “why haven’t I heard of this company,” the email offers an answer. Management changes, delays, a new sales person stepping in — it’s a ready-made excuse for every inconsistency. This kind of trust-manipulation narrative is a core pattern across every type of scam email targeting store owners — the framing changes, the mechanism doesn’t. It triggers empathy and suppresses skepticism simultaneously
“Check the enclosed bank detail” is the tell.
Legitimate buyers do not send their bank details to a supplier before an order is confirmed. That’s not how B2B purchasing works. This phrasing signals one of two things: the attacker wants to route a future payment to a mule account, or they’re baiting the recipient into sharing their own payment information in the proforma invoice they’re requesting.
Either direction involves money moving to the wrong place.
The greeting has no name.
“Dear,” — nothing after it. No name, no store name, no order reference that connects to any actual transaction. This is a bulk scam email. The content was not written for this recipient.
The language doesn’t match the claimed identity.
“Please refer enclose attach PO for your product. Kindly provide the PI as soon as possible. Submission will be courier to you later.”
This is not how a Sales Executive at a technology company in Qatar writes procurement correspondence. The grammar, the phrasing, and the sentence construction are consistent with mass-produced scam templates — not professional business communication.
Step 3 — The Attachment (Without Opening It)
The attachment is named EDIT PI-74625463.rar and weighs 24.1 KB.
PI stands for Proforma Invoice. The name is designed to look like a legitimate invoice reference. The format — .rar — is not.
Proforma invoices, purchase orders, and business correspondence travel as PDF files. Occasionally DOCX. Never as .rar archives. There is no legitimate reason for a business document to be compressed in a RAR format before being emailed.
What a .rar file can contain: executables, scripts, or malware disguised with misleading filenames. A common technique is double-extending a file — naming it Invoice.pdf.exe so it appears to be a PDF in the archive view, but executes as a program when opened. The 24.1 KB file size is consistent with a dropper payload — a small initial file that installs or downloads a larger malicious component from a remote server after execution.
Without opening the archive, the specific payload cannot be confirmed. That analysis was not performed, and the file should not be opened on any machine connected to business accounts or payment platforms. What can be confirmed is the context: a .rar attachment from a mismatched sender, using a social engineering pretext, requesting financial engagement. That profile does not require the file to be opened to reach a conclusion.
If you want to check a suspicious file without opening it, upload it directly to VirusTotal — it scans against 70+ antivirus engines with no local execution required.
Step 4 — What This Attack Is Actually Doing
This is not a standard phishing email with a link to a fake login page. Unlike the Shopify verification email we broke down previously — where the attack ran through a redirect chain to a silent tracking endpoint — there are no URLs in this email’s body to analyze. The attack runs on two tracks simultaneously.
Track 1 — Malware delivery via attachment.
The .rar file is the technical attack vector. If extracted and opened, the payload would most likely install a remote access trojan (RAT), keylogger, or credential-stealing malware on the recipient’s machine. These tools are designed to harvest stored passwords — email, Shopify admin, banking portals, payment processors — without any visible indication that anything went wrong. The attacker gains quiet access rather than triggering an obvious alert.
Track 2 — Payment fraud via social engineering.
Even without the attachment, the email is structured to initiate a fake commercial relationship. If the recipient replies, the conversation escalates: fabricated purchase order documents arrive, followed by bank transfer details pointing to a mule account. Alternatively, the attacker collects the recipient’s own proforma invoice — which contains their real banking information — and uses it in downstream fraud.
The two tracks are not mutually exclusive. Both can run from the same email. The first contact is designed only to produce a response: a reply, or a double-click on the archive. Nothing more is needed to start either chain.
Step 5 — What Would Happen If You Engaged
If you replied:
The attacker sends follow-up documents — typically convincing PDF purchase orders with real-looking company letterheads and reference numbers. They ask for a proforma invoice in return. Your PI contains your bank account details. Those details are then used to impersonate you to another party, or the attacker simply waits until goods are shipped against a payment that never arrives.
In a variation of this attack, the “bank details” they mention in the first email are for an account they control. The pitch is: “We’ve updated our payment details due to the management change — please use these going forward.” If the recipient has any existing supplier relationship with a similar name, this framing is particularly effective.
If you opened the .rar:
A credential-harvesting payload installs silently. Shopify admin credentials, Google account access, email login, saved browser passwords — anything accessible on that machine is at risk. The attacker typically doesn’t act immediately. They log in quietly, monitor activity, and act when something valuable is available: a payout threshold, a large incoming order, an active ad campaign with budget attached.
In either case, the damage happens after the first move. This email is just the opening.
Key Takeaways
- A company’s email domain is the only identity that matters. Display names are decorative.
ikunev79@abv.bgclaiming to represent a Qatari technology company is a mismatch that ends the conversation. Always check the actual sending domain — not the name shown in the inbox. - “RE:” in the subject line from an unknown sender is not a reply — it’s a manipulation tactic. Check your sent folder. If there’s no original email, the prefix was added to manufacture familiarity. Treat it as a red flag, not a cue to recall a conversation.
.rar,.zip, and.7zattachments from unknown senders are a red line. Business documents don’t need to be compressed in archive formats before being emailed. This format choice exists to obscure file contents and bypass attachment scanners. Don’t extract, don’t open, don’t forward.- “Check our bank details” in a first contact email is not a procurement step — it’s fraud framing. Legitimate buyers don’t initiate relationships by routing payment information. This phrase signals either an advance fee setup or a payment redirection attempt.
- If the email arrived at an old or migrated address, the sender got it from a scraped list. That means the targeting is not personal — this is volume outreach. It also means your current contact information may not be in their database. Don’t reply to update them
- Upload the attachment to VirusTotal if you want to check the file without executing it — do this from a browser only, do not extract or run the archive locally
Final Verdict
| Category | Result |
| Sender legitimacy | Fake — Bulgarian free email, no connection to claimed Qatari company |
| Attachment safety | High risk — .rar format from mismatched sender, not opened or verified |
| Immediate risk | High — dual-vector attack: malware delivery and payment fraud setup |
| Strategic intent | Credential harvesting and/or advance fee / payment redirection fraud |
| Targeting method | Bulk outreach via scraped email database |
What to Do If You Received This Email
- Do not reply — any response confirms your address is active and monitored
- Do not download or open the
.rarattachment on any device - If you opened the attachment before reading this: change passwords on email, Shopify, and any payment platform immediately, from a different device
- Mark as spam and delete
- If you received it at a business address, check whether the same address appears in public databases or old web listings — and consider whether it needs to be updated
- Forward the email to your email provider’s abuse team if you want to report it

Stay Safe With EmailClarity
Every week, we break down real scam emails targeting online store owners — the kind that land in your inbox pretending to be Shopify support, fellow entrepreneurs, or marketing geniuses who can triple your sales overnight.
Use our email analysis tool at email-clarity.com to scan suspicious emails instantly, or forward anything sketchy to blog@email-clarity.com and we’ll give it our honest take.
The more emails we collect, the more store owners we can help. Your sketchy inbox is someone else’s warning sign.
Stay sharp out there.
— The EmailClarity Team
Leave a Reply